Microsoft Corp. in the present day issued software program updates to plug not less than 139 safety holes in varied flavors of Home windows and different Microsoft merchandise. Redmond says attackers are already exploiting not less than two of the vulnerabilities in energetic assaults in opposition to Home windows customers.
The primary Microsoft zero-day this month is CVE-2024-38080, a bug within the Home windows Hyper-V part that impacts Home windows 11 and Home windows Server 2022 techniques. CVE-2024-38080 permits an attacker to extend their account privileges on a Home windows machine. Though Microsoft says this flaw is being exploited, it has provided scant particulars about its exploitation.
The opposite zero-day is CVE-2024-38112, which is a weak spot in MSHTML, the proprietary engine of Microsoft’s Web Explorer internet browser. Kevin Breen, senior director of risk analysis at Immersive Labs, stated exploitation of CVE-2024-38112 possible requires using an “assault chain” of exploits or programmatic adjustments on the goal host, a la Microsoft’s description: “Profitable exploitation of this vulnerability requires an attacker to take extra actions previous to exploitation to arrange the goal surroundings.”
“Regardless of the dearth of particulars given within the preliminary advisory, this vulnerability impacts all hosts from Home windows Server 2008 R2 onwards, together with purchasers,” Breen stated. “Resulting from energetic exploitation within the wild this one must be prioritized for patching.”
Satnam Narang, senior workers analysis engineer at Tenable, known as particular consideration to CVE-2024-38021, a distant code execution flaw in Microsoft Workplace. Assaults on this weak spot would result in the disclosure of NTLM hashes, which could possibly be leveraged as a part of an NTLM relay or “move the hash” assault, which lets an attacker masquerade as a reliable consumer with out ever having to log in.
“One of many extra profitable assault campaigns from 2023 used CVE-2023-23397, an elevation of privilege bug in Microsoft Outlook that might additionally leak NTLM hashes,” Narang stated. “Nonetheless, CVE-2024-38021 is proscribed by the truth that the Preview Pane will not be an assault vector, which signifies that exploitation wouldn’t happen simply by merely previewing the file.”
The safety agency Morphisec, credited with reporting CVE-2024-38021 to Microsoft, stated it respectfully disagrees with Microsoft’s “essential” severity score, arguing the Workplace flaw deserves a extra dire “important” score given how straightforward it’s for attackers to take advantage of.
“Their evaluation differentiates between trusted and untrusted senders, noting that whereas the vulnerability is zero-click for trusted senders, it requires one click on consumer interplay for untrusted senders,” Morphisec’s Michael Gorelik stated in a weblog put up about their discovery. “This reassessment is essential to mirror the true threat and guarantee sufficient consideration and sources are allotted for mitigation.”
In final month’s Patch Tuesday, Microsoft fastened a flaw in its Home windows WiFi driver that attackers might use to put in malicious software program simply by sending a susceptible Home windows host a specifically crafted knowledge packet over an area community. Jason Kikta at Automox stated this month’s CVE-2024-38053 — a safety weak spot in Home windows Layer Two Bridge Community — is one other native community “ping-of-death” vulnerability that must be a precedence for highway warriors to patch.
“This requires shut entry to a goal,” Kikta stated. “Whereas that precludes a ransomware actor in Russia, it’s one thing that’s outdoors of most present risk fashions. One of these exploit works in locations like shared workplace environments, motels, conference facilities, and anyplace else the place unknown computer systems is likely to be utilizing the identical bodily hyperlink as you.”
Automox additionally highlighted three vulnerabilities in Home windows Distant Desktop a service that allocates Shopper Entry Licenses (CALs) when a shopper connects to a distant desktop host (CVE-2024-38077, CVE-2024-38074, and CVE-2024-38076). All three bugs have been assigned a CVSS rating of 9.8 (out of 10) and point out {that a} malicious packet might set off the vulnerability.
Tyler Reguly at Forta famous that in the present day marks the Finish of Assist date for SQL Server 2014, a platform that based on Shodan nonetheless has ~110,000 cases publicly accessible. On prime of that, greater than 1 / 4 of all vulnerabilities Microsoft fastened this month are in SQL server.
“A whole lot of firms don’t replace rapidly, however this will depart them scrambling to replace these environments to supported variations of MS-SQL,” Reguly stated.
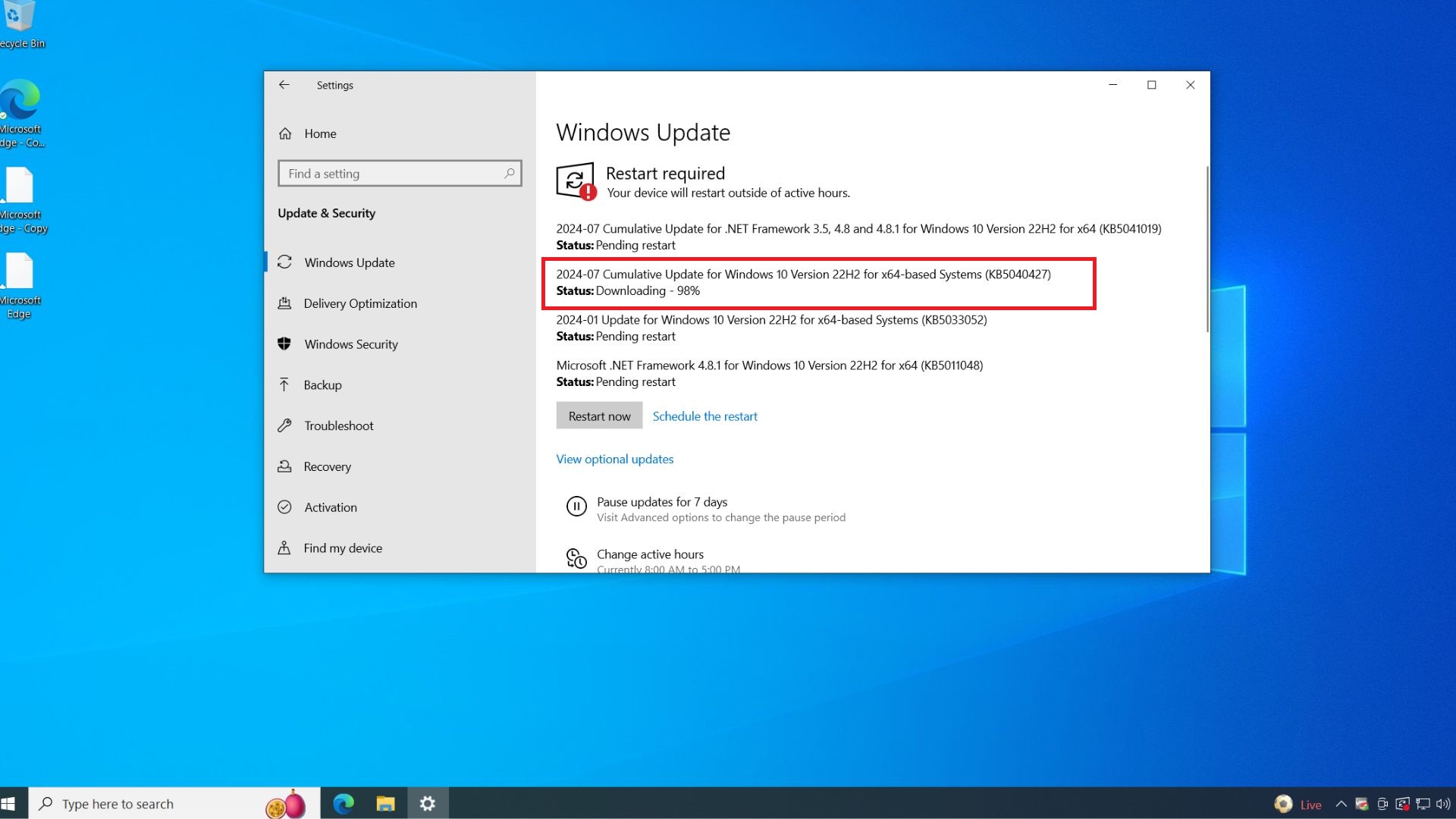
It’s a good suggestion for Home windows end-users to remain present with safety updates from Microsoft, which might rapidly pile up in any other case. That doesn’t imply you must set up them on Patch Tuesday. Certainly, ready a day or three earlier than updating is a sane response, on condition that typically updates go awry and often inside a number of days Microsoft has fastened any points with its patches. It’s additionally good to again up your knowledge and/or picture your Home windows drive earlier than making use of new updates.
For a extra detailed breakdown of the person flaws addressed by Microsoft in the present day, take a look at the SANS Web Storm Middle’s listing. For these admins liable for sustaining bigger Home windows environments, it usually pays to control Askwoody.com, which regularly factors out when particular Microsoft updates are creating issues for numerous customers.
As ever, for those who expertise any issues making use of any of those updates, think about dropping a word about it within the feedback; chances are high respectable another person studying right here has skilled the identical subject, and perhaps even has an answer.